The cloud computing market continues to grow and is expected to reach an estimated 496 billion USD in 2022 across various domains, as per Statista. AWS, Azure, and Google currently dominate the market with their cloud platforms. Organizations, big or small, are investing in the cloud like never before, thus requiring robust cloud security and governance for their data.
However, the transition to the cloud brings new security challenges. Due to cloud services being available online, anyone with the proper credentials can access them. And with much enterprise data availability, it easily attracts hackers who want to compromise the systems by finding loopholes and exploiting them to their benefit.
Apple, Meta, Twitter, and many more tech giants have all disclosed cybersecurity attacks this year. Unfortunately, the situation is the same for multi-scaled businesses – damages worth millions happen because of poorly designed cloud security approaches.
One of the main problems with assessing cloud computing security issues is understanding how cyber attacks happen, their consequences, and how to prevent them. This blog will look at some cloud computing security threats businesses face, how to prevent cloud attacks, and best practices for cloud security.
Let’s dive right in.
What are the cloud computing security threats that companies face
With the mass adoption of cloud computing, the following are a few cloud computing security threats that companies face.
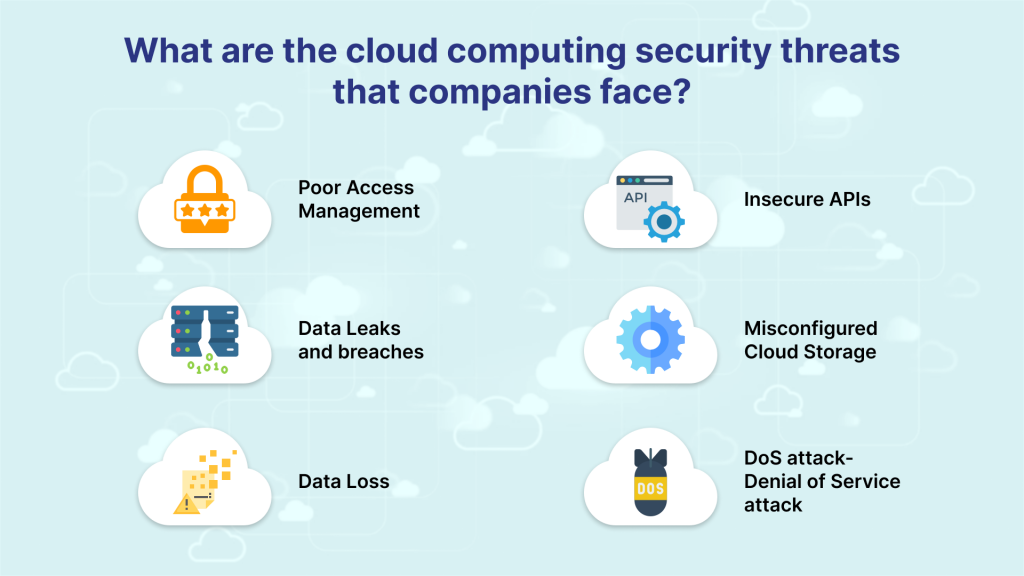
1. Poor Access Management
Poor access management is the primary cloud computing risk businesses face, which is why hackers often target it.
Many companies recently experienced attacks on cloud computing where massive data breaches over the past few years, including account credentials, occurred due to improper crisis management and ineffective data management.
2. Data Leaks and Breaches
A data leak happens when the information is accessed and extracted without proper authorization, which may be confidential information that can be sold or held for ransom. It usually occurs when a cybercriminal exploits a security threat, gets access to the system, and extracts the desired data.
Twilio, earlier in August 2022, experienced unauthorized access to information through a social engineering attack designed to steal credentials of its Authy two-factor authentication (2FA) service.
3. Data Loss
One cloud security risk that is hard to predict and even harder to handle is data loss. Some common reasons for data loss include data alteration, where information changes away from the original and cannot be reverted to the previous state, loss due to issues on the cloud provider’s side; and deletion, where information erasure occurs with no backups to restore.
4. Insecure APIs
The availability of multiple APIs can be a significant cloud security risk as they are involved in gathering data from devices that the software runs on. In addition, sometimes, the configurations of the API may not be up to the standards and contain several flaws that can compromise integrity. Some common issues are anonymous access, lack of user controls, reusable tokens, and passwords.
An example of an insecure API in action is the widely publicized Cambridge Analytica Scandal, where Facebook API had access to user data, and Cambridge Analytica used it for its benefit.
5. Misconfigured Cloud Storage
A misconfigured cloud can be fodder for cyber criminals making the cloud servers vulnerable to breaches. A few types of them include mismatched access management when an unauthorized person gets access to sensitive data, open data access where confidential data is left open and requires no authorization, and default cloud storage settings where there is standard access management with availability available to all.
6. DoS attack- Denial of Service Attack
A DoS attack stops users from accessing the application or disrupting the workflow, which is like messing up with the service-level agreement between the company and the customer. This can lead to damage to the credibility of the company.
Moving on, let us see how you can secure cloud services by learning how you can prevent them in the first place.
How much does App Maintenance Cost
How to prevent cloud attacks
Prevention is the best cure. Therefore, organizations must maintain robust and proactive security measures that protect their cloud-hosted resources to prevent cyberattacks and threats.
The following tips can help prevent cloud attacks and elevate an organization’s preparedness to mitigate any threat.
1. Multi-factor Authentication (MFA)
MFA is critical to protect user accounts from hackers. A traditional username and password combination may be insufficient as hackers can easily compromise it to log in and access your business data and applications.
MFA can be the cheapest and most effective security control to keep hackers from accessing your cloud applications.
2. Limit User Access to Cloud Security
If multiple users can access a company’s cloud storage, the first thing businesses can do is set up proper authorization levels. This ensures that employees can only view or manipulate the applications or data necessary to do their job.
It also prevents the employee from accidentally editing the information they are not authorized to access and protects businesses from hackers who have stolen the employee’s credentials.
3. Backup Data Regularly
Backing up data is the best way to protect businesses against configuration errors or malware that may compromise or erase them. Unfortunately, many companies have experienced the devastating effects of losing data through negligence.
Due to a clerical error, Toy Story 2 was erased accidentally during production. It was recovered with great difficulty later on. Though the movie wasn’t on cloud storage, the story shows the importance of having backups.
Companies cannot afford to store confidential information just anywhere as it is essential to set up automatic backup and recovery on separate servers. Also, backups can be stored in physical drives in case online servers fail.
4. Conduct Employee Training Workshops on Cloud Security and Anti-Phishing
Hackers can gain access to secure information by stealing employee credentials through social engineering, phishing, spoofing websites, and social media spying. Training can teach employees about the dangers and safety practices implemented by the company, and they can stay protected against account hijacking, avoid malware and avoid configuration errors.
Most successful companies know that employee training is the way to keep everyone on the same page about company policies. In addition, cloud security is a topic most employees must understand about. Above all, people must familiarize themselves with the software they work on and the existing loopholes.
5. Test Regularly with the Help of Cybersecurity Professionals
One of the best ways to protect the cloud is penetration testing, a security practice designed to identify and address vulnerabilities in your products or services and minimize cloud computing security threats.
Move the data to another server if necessary before you begin and fix the errors that may come up after the test. It is advised to always take backups of company data without disrupting the ordinary course of business.
6. Increase Network Bandwidth to Prevent DDoS Attacks
Distributed denial of service (DDoS) attacks are one of the common risks associated with cloud computing. Hackers may try to block access to the businesses’ cloud computing with connection requests from false accounts.
Increasing the company’s network bandwidth can withstand the rush of requests. Businesses can also benefit from having a backup internet connection.
Now what to look for in cloud security? Well, businesses can follow the cloud security tips given below.
Cloud Security Best Practices
Cloud security is constantly evolving, and the following practices can ensure the security of cloud environments.

The following are some best practices for cloud security.
App Development Cost: The Definitive Guide
1. Choose a Trusted Provider
With abundant options available, it is necessary to pick the right cloud service provider who delivers the best in-built security protocols and conforms to industry standards and compliances.
Compare the security measures offered by various providers and mechanisms used to protect applications and data. Also, enquire about the level and mode of support services they offer.
2. Understand Your Shared Responsibility Model
When businesses consider a particular cloud vendor, they should review the policies about shared security responsibilities. Also, understand the intricacies of handling various aspects of cloud security to prevent miscommunication.
3. Deploy an Identity and Access Management Solution
A high-quality identity and access management solution can help mitigate any threat. Ensure that you enforce role-based permissions and multi-factor authentication, which can help reduce the risk of losing or leaking sensitive information.
Deploy a solution that can work best in a hybrid environment that includes private data centers and cloud deployments.
4. Train your Staff
Businesses must train all workers to spot threats early on, create strong passwords, identify any social engineering attacks, and respond to them.
You should explain the potential risks and keep them updated about the latest threats and possible countermeasures.
5. Secure the endpoints
Have an in-depth strategy to secure your endpoints, including firewalls, anti-malware, intrusion detection, and access control.
Also, automation tools can be used, such as endpoint detection and response tools and endpoint protection platforms, which can continuously monitor and record automated responses from time to time.
6. Implementing Encryption
Encryption is the key to any cloud security strategy. Businesses must encrypt data in public cloud storage. Multiple cloud computing providers offer encryption and essential management services.
Find a good encryption product that works seamlessly with your existing work processes and eliminates the need for end users to comply with encryption policies.
7. Double-check Compliance Requirements
Organizations that wish to use a cloud computing service and collect personally identifiable information must review compliance requirements and ensure that they meet all data security needs.
8. Consider a CASB Vendor
If a company does not have cloud expertise or existing security services that do not support a cloud environment, you can bring in Cloud access security brokers (CASBs). They are tools that help enforce cloud security policies and can be used when businesses have multiple cloud computing services from different vendors.
9. Conduct Audits and Penetration Testing
Regular security audits can be done that include an analysis of all capabilities. For example, access logs can be audited to ensure that only appropriate and authorized personnel can access sensitive information and applications on the cloud.
Additionally, penetration tests can be run from time to time to determine if existing cloud security efforts are sufficient to protect data and applications.
10. Enable security logs
In addition to audits, businesses must enable logging features, too, for their cloud solutions. It helps administrators keep track of users making changes in the environment. Even if an intruder gains access and changes, the logs show their activity and can be remediated quickly.
Summing Up
Is your cloud secure enough?
Cloud security is an integral part of cloud application development and management. Proper security methodologies can protect your business from any attack and increase operational efficiency and simplicity.
Cloud Storage can be tricky if not handled well, and some solutions can help you mitigate risks and provide better cover.
End-to-end compliance technologies and cybersecurity penetration tests from time to time can help businesses from security breaches. Something that digital service providers like Ailoitte can help bring in your app data hosting on a cloud with ample storage, backup, affordable pricing, and, most importantly, robust security.
This ensures that when your company moves from local servers to the cloud, they have zero loopholes and lags. Contact us today for more information.
FAQs
One of the biggest threats is data loss or leakage, which is a significant concern for companies citing that it is one of the main security issues. Regular backups must be a core practice in a data loss event.
– There are several risks to consider
– Poor Access Management
– Data Loss
– Insecure APIs
– Data Breaches
– Cloud Misconfiguration
– Denial-of-service (DoS) Attacks
– Malware Infections
– Compliance Violations
The following are the best ways to protect data in a cloud
– Set up backup and recovery options
– Encrypt data
– Set proper user permissions
– Set up stronger passwords
– Employ multi-factor authentication
– Secure end-user devices
– Avoid uploading confidential data
– Run Tests
Cloud security management is end-to-end procedures and technology that are clubbed to address external and internal threats to business security when their data is in the cloud.















.png)
.png)
.png)


Leave a Comment